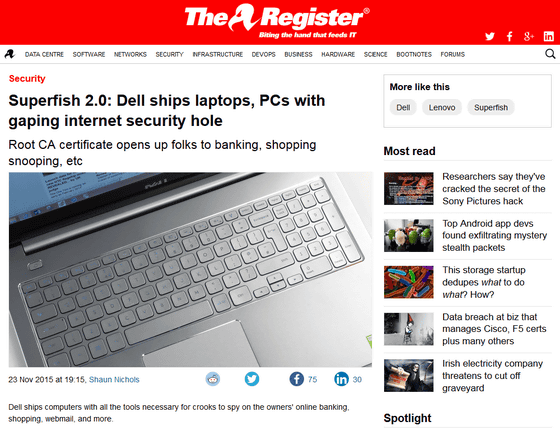
There is a danger that Dell notebook PCs are equipped with the same root certificate & secret key and are subject to man-in-the-middle attacks
In February 2015It turned out that adware called "Superfish" was preinstalled on Lenovo PC. Since the signature (secret key) of the certificate authority (CA) is kept in the program, if a secret key is taken out, a malicious attacker can attack and it becomes all-you-can, know that it is a security hole rather than adware,Lenovo himself provided an automatic deletion toolThere was a turmoil of becoming to do, but this time it became clear that a similar situation is occurring on Dell PC.
Superfish 2.0: Dell ships laptops, PCs with gaping internet security hole • The Register
http://www.theregister.co.uk/2015/11/23/dude_youre_getting_pwned/
Dell does a Superfish, ships PCs with easily cloneable root certificates | Ars Technica
http://arstechnica.com/security/2015/11/dell-does-superfish-ships-pcs-with-self-signed-root-certificates/
Encrypting and exchanging dataTLS / SSL communicationThe basic principle is that "the browser has a root certificate of a trusted certificate authority (CA)" "CA's signature (secret key) is secret" "The server keeps the secret key secret" It is a major premise that we are protected. However, in the case of Superfish preinstalled on Lenovo PC, the secret was not kept because the secret key was in the program and it was possible to retrieve it.
This time, the matter discovered by Dell PC is similar to this, already some "Superfish 2.0It is also expressed.
It was not adware that found on Dell PC, but self-issued root certificate "EDellRoot". The eDellRoot contains a secret key and can be retrieved by using the tool,Man-in-the-middle attackIt was in a state to be able to trap on.
The fact that this certificate is preinstalled has been reported by Kevin Hicks who purchased XPS 15 (active in the name of "rotorcowboy" in Reddit) and Joe Node who purchased Inspiron 5000, and rotorcowboy Mr. Ms. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr. Mr
Dell ships laptops with rogue root CA, exactly like what happened with Lenovo and Superfish: technology
https://www.reddit.com/r/technology/comments/3twmfv/dell_ships_laptops_with_rogue_root_ca_exactly/
Joe Nord personal blog: New Dell computer comes with a eDellRoot trusted root certificate
http://joenord.blogspot.in/2015/11/new-dell-computer-comes-with-edellroot.html
Mr. NodeCertificate Manager tool"EDellRoot" confirmed with. It is installed as a "trusted root certificate".
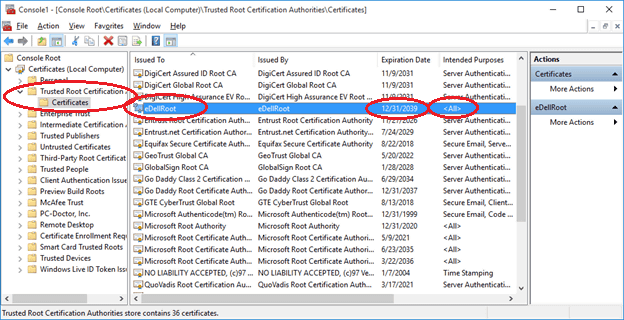
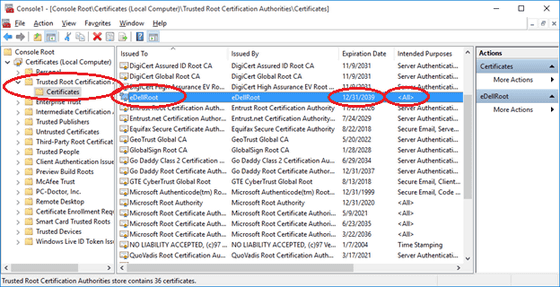
The issuer / publisher is eDellRoot, the creation date is April 7, 2015, the expiration date is December 31, 2039. Mr. Node saw the notation "I have a secret key corresponding to this certificate" that marked red, and it seems that it came to me as if it is strange.

Dell replied that "There is no threat to the system" in the inquiry from Hicks.
@rotorcowboyIt's a Dell trusted certificate that is not in the OS. It does not cause any threat to the system, so we do not recommend recommend-1
- DellCares (@ DellCares)2015, November 22
In Thr Register that we checked "eDellRoot" with Inspirion 15 purchased in July and was in the office, it was confirmed that even if eDellRoot is deleted using the certificate manager tool, it will be revived.
Superfish 2.0 worsens: Dell's dodgy security certificate is an unkillable zombie • The Register
http://www.theregister.co.uk/2015/11/23/dell_security_nightmare_gets_worse/
According to Duo Security, plug-in will reinstall if eDellRoot has been deleted, so first you need to delete "Dell.Foundation.Agent.Plugins.eDell.dll" And that. In conjunction with this plug-in, eDellRoot seems to be installed to receive encrypted telemetry requests, Duo Security says, "OEM manufacturers' disturbing trend is emerging. Originally these certificates Change, especially the addition of the root certificate needs to be done carefully, but the OEM manufacturer seems to repeat the same thing over and over again without learning the past mistakes. "
In addition, Ken · White has created a site to judge whether your PC is OK. When accessing the URL described in this tweet, you can confirm that an error indicating that there is a problem with the certificate is OK, and if the page is displayed you can see that the eDellRoot certificate is installed.
If you have a recent XPS 15 running Windows and can load my page:https://t.co/qExUHLQwH0Then you're vulnerable to Dell's bogus root cert.
- Kenn White (@ kennwhite)2015, November 23
At the moment when browsing with XPS 15, Inspirion 5000, etc., it is immediate measures to use Firefox which has a separate certificate list.
· Continued
Dell unveils removal tool for root certificate "eDellRoot" pointed out by vulnerability - GIGAZINE

Related Posts:
in Security, Posted by logc_nt