Pointed out that the data security of modern automobiles to say high-tech equipment is too poor

ByJosi Kraft
Automobiles have the character as "high-tech equipment" in that they are equipped with many sensors on the latest cars and collect data and actively use it. However, it is denounced by American politicians that "data management in the automotive system is sloppy."
2015-02-06_MarkeyReport-Tracking_Hacking_CarSecurity 2. pdf
(PDF file)http://www.markey.senate.gov/imo/media/doc/2015-02-06_MarkeyReport-Tracking_Hacking_CarSecurity%202.pdf
Senator: Car hacks that control steering or steal driver data way too easy | Ars Technica
http://arstechnica.com/security/2015/02/senator-car-hacks-that-control-steering-or-steal-driver-data-way-too-easy/
Senator Edward Markey of the United States is the automaker of BMW, Chrysler, Ford, GM, Honda, Hyundai, Jaguar Land Rover, Mazda, Mercedes-Benz, Mitsubishi, Nissan, Porsche, Subaru, Toyota, Volkswagen Audi, Volvo We sent a letter on automobiles and data security to the 16 major companies and gathered the results as a report.
All 16 companies are exchanging data using wireless technology for car navigation system and tire pressure measurement etc. But stillWEPWe found that there are manufacturers that use low security level encryption technology such as. When asked how much Senator Markey is aware of the hacking damage of wireless communication that occurred in the past, most automakers did not fully recognize the hacking damage that occurred in their car system, or immediately answered It seems that it was a situation that it can not be done.

According to Senator Markey's report, by rewriting the firmware used for CD / DVD player, Bluetooth unit and other onboard equipment in the current car system to remodeling software, it can exploit in-vehicle network system (CAN) There is already a way to transmit codes, and by misusing this it is possible not only to steal automobile information but even to operate from the outside. Therefore, although car manufacturers should pay more attention to security in the car system, it is pointed out that automobile manufacturers' consciousness is generally very low, such as answers that seems to be unfamiliar to their systems are returned.
Many automobile manufacturers not only include basic information such as vehicle speed, gasoline consumption, tire pressure, window lock status, but also vehicle position information measured at regular time intervals, destination information retrieved by navigation, We also acquired data on emergency situations that could lead to accidents such as stops, sudden stops and sudden departures, and that information volume is increasing year by year.

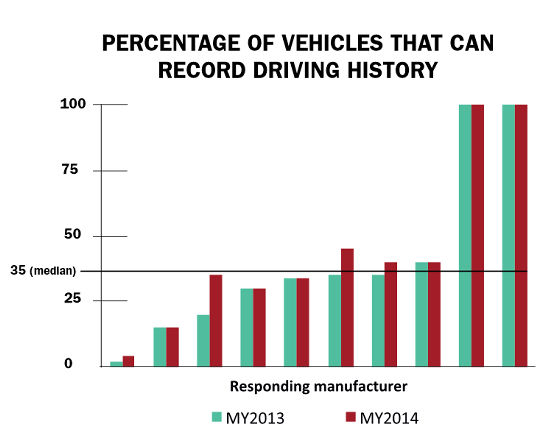
This is a graph showing the percentage of records of the driving situation among the products of 10 major manufacturers. Although there is a difference in enthusiasm for data acquisition by manufacturers, there is no manufacturer that 2014 (red) has reduced the number of models to acquire data than 2013 (green).
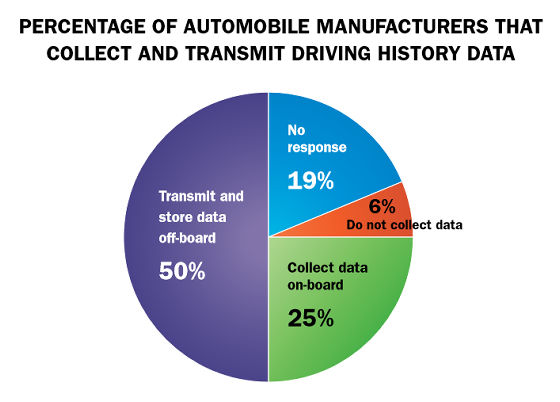
Meanwhile, many manufacturers are keen to collect and store data. Only one manufacturer responded that they did not collect car data, and 12 companies gathered data except for the three manufacturers who refused to answer, of which eight companies received data from the inside of the car It transfers it to the server and keeps it.
Senator Marquee, when asking how to use the collected data, states the reasons why "we are making use of it to improve the user experience", but we are disclosing sufficient information about how to use it to the user Nevertheless, the user can further collect and use informationopt outI can point out that there are many problems such as not being able to do.
·bonus
Developer event with a strong sense as hacker's "arm test"DEF CON"As demonstrated by" Hacking the Prius and steering on the notebook PC "published in" It is clear that the current car is a software-controlled high-tech device. As automobile driving technology evolves and spreads in the future, it is expected that the color of high-tech equipment will become darker, but the security management system at hand seems to be poor than I imagined.
The way the Prius is "hacked" can be checked with the following movie.
Digital Carjackers Show Off New Attacks - YouTube
Related Posts:







