IBM pointed out vulnerabilities related to Android application's encryption key, the patch was distributed only to Android 4.4 and about 86% of the total remains risked

ByN Kauscher
IBM's Application Security Research Team is a database that serves as a repository for storing private and public key pairs and public key certificates of Android applicationsKeyStorePointed out the vulnerability. Currently the patch for this vulnerability is only released for Android 4.4,86.4% of the whole Android terminalAre still in danger of being injured.
Android KeyStore Stack Buffer Overflow
http://securityintelligence.com/android-keystore-stack-buffer-overflow-to-keep-things-simple-buffers-are-always-larger-than-needed/

Serious Android crypto key theft vulnerability affects 86% of devices | Ars Technica
http://arstechnica.com/security/2014/06/serious-android-crypto-key-theft-vulnerability-affects-86-of-devices/
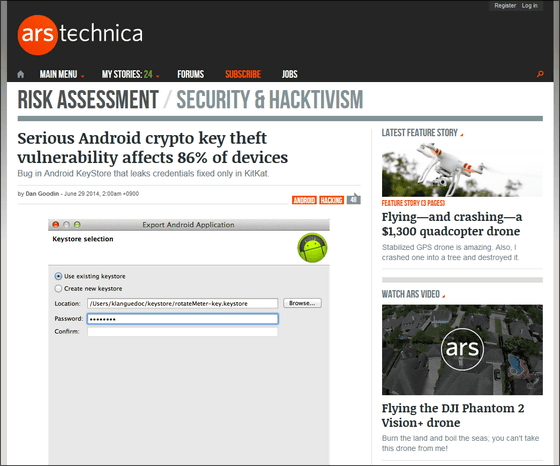
According to IBM 's application security research team, when an attacker uses KeyStore vulnerability, it can be used for applications such as money banking applications such as internet banking applicationsVPNIt is an identification number when using a connection application, a credit card or a cash cardPINEncryption keys can be obtained from various applications such as applications that use codes and fingerprint authentication functions. This vulnerability is due to a bug at development time, and an attacker is able to use malicious code that leaks the encryption key via an application using KeyStore.
In addition, IBM's security advisor said, "Google is stack-basedBuffer overflowWe distributed repair patch concerning Android 4.4 only ", and also reveals that KeyStore vulnerability still remains on Android terminal with OS version other than 4.4.

ByMarsmetn tallahassee
However, there are some technical hurdles for attackers to exploit this vulnerability. Android OSData execution preventionYaRandomization of address space arrangementAnd these are making it difficult for an attacker to exploit vulnerabilities to launch malicious attacks. Also, in order for an attacker to launch an attack using vulnerability, it is necessary to install an application containing malicious code on a terminal equipped with an Android 4.4 or earlier OS, and it is easy to clear these It is also pointed out that it is not. However, the vulnerability still exists on the KeyStore,Under the App Store and Google Play security level revealed the fact that users can not be protected from explosion and sophisticated malwareGiven that it is going to be, I'd like the Google patch to be released as soon as possible.
When Ars Technica asked Dan Wallach, professor at Rice University's computer science department, for an opinion on this vulnerability, Wallach said, "If we have a vulnerability in KeyStore, we will pretend others' Since you can use the application without logging in or you can use the application without login information it is easy to use Internet banking application that prompts you to enter account information at the time of login.In addition, If the electronic certificate is stolen, it will be possible to disable users from connecting to the Internet, and various attacks using this vulnerability will be anticipated. "
"The vulnerability of KeyStore could also create other threats.This vulnerability could allow cybercriminals to access the resource part of the OS called Android and may therefore perform more influential cryptographic operations What is saidViaForensicsMr. Pau Oliva, senior security engineer.

ByDaniel
In Japan,NTT docomoYaAuAnnounces that it updates some terminals to Android 4.4.
2014/07/11 21:20 Addendum
Android application encryption key vulnerability appeared to be only Android 4.3, IBM's application security research team is updating information.

Related Posts:
in Software, Smartphone, Posted by logu_ii