Russian government-backed hackers infiltrate multiple home routers and steal passwords.

The British government and private security companies have warned that Russian hacker groups are exploiting router vulnerabilities to hijack communications.
APT28 exploit routers to enable DNS hijacking operations | National Cyber Security Center - NCSC.GOV.UK
Frostarmada forest blizzard dns hijacking
https://www.lumen.com/blog-and-news/en-us/frostarmada-forest-blizzard-dns-hijacking
According to the UK government's cybersecurity arm, NCSC, and security firm Lumen, a Russian hacking group known as 'Fancy Bear' or 'APT28' exploited vulnerabilities in MikroTik and TP-Link routers to carry out 'man-in-the-middle attacks' to eavesdrop on communications. The NCSC stated that it 'almost certainly assesses APT28 as a unit under the Russian military intelligence agency (GRU).'
Lumen explains that some routers have vulnerabilities related to their DNS systems. DNS is a system that manages the mapping and translation of human-readable domain names, such as 'gigazine.net,' to computer-readable IP addresses. According to Lumen, although the vulnerabilities of DNS are well known, some products are slow to address them.
APT28 first exploited a vulnerability in the router to gain remote administrator privileges and changed the router's default DNS settings. They configured it to refer to a virtual private server controlled by the attacker. As a result, when a user accesses an email app or any login page, the malicious DNS server redirects them to a different IP address owned by APT28.

The only indication of this attack was a pop-up warning stating that the user was attempting to connect to an untrusted source. If the user ignored the warning and proceeded, APT28 forwarded the request to a legitimate service through a proxy, collecting data at an intermediate point and gathering data associated with the target account by passing a valid OAuth token. This allowed APT28 to access authentication credentials such as the OAuth token.
This method initially targeted specific users, but it spread rapidly from late 2025 to early 2026, with over 290,000 IP addresses observed sending DNS requests to DNS servers managed by APT28 at least once in a single month. However, when narrowed down to IP addresses that interacted with DNS servers at least five times, the number drops to about 40,000, and when narrowed down to 10 times, it drops to about 18,000. Lumen considers this number of 18,000 to have 'moderate confidence' and estimates it to be the actual number of victims.
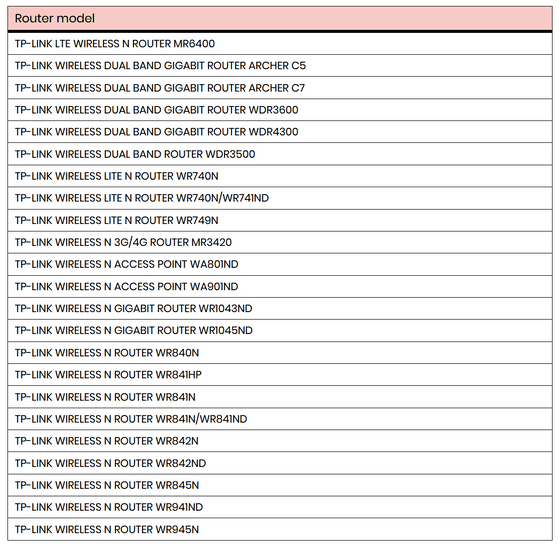
The following are the TP-Link router models that APT28 exploited. The NCSC, which compiled this
The FBI announced it has neutralized the portion of the network used in the attack that was deployed in the United States. Lumen stated it disrupted the botnet as part of a coalition that included the FBI. The agencies involved in the investigation are urging users to update their router software.
Related Posts: