It turns out that a Chrome extension with over 900,000 downloads is stealing conversation data and browser browsing history from ChatGPT and DeepSeek

Researchers at security firm OX Security have discovered that two Chrome extensions, with a combined total of over 900,000 downloads, are stealing user conversation histories, including those between users and the AI, as well as their Chrome browser browsing history.
Malicious Chrome Extensions Steal ChatGPT Conversations
Two Chrome Extensions Caught Stealing ChatGPT and DeepSeek Chats from 900,000 Users
https://thehackernews.com/2026/01/two-chrome-extensions-caught-stealing.html
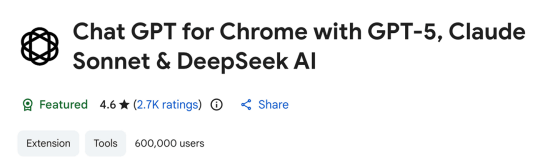
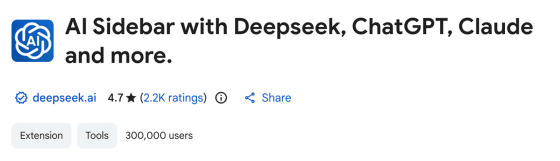
The two Chrome extensions found to contain malware this time are ' Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI ' and ' AI Sidebar with Deepseek, ChatGPT, Claude and more .' Both add a sidebar to the top of any website, allowing you to chat with popular chat AIs at any time.
At the time of the issue's discovery, 'Chat GPT for Chrome with GPT-5, Claude Sonnet & DeepSeek AI' had over 600,000 downloads, while 'AI Sidebar with Deepseek, ChatGPT, Claude and more' had over 300,000 downloads. The former in particular had earned a 'Featured' badge in the Chrome Web Store.
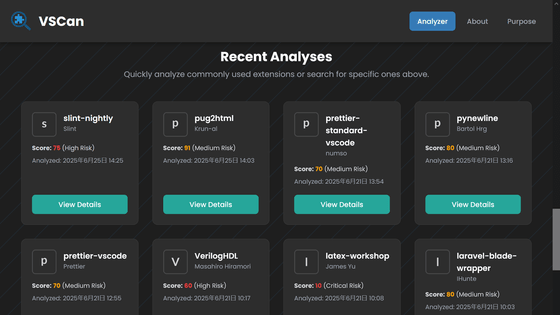
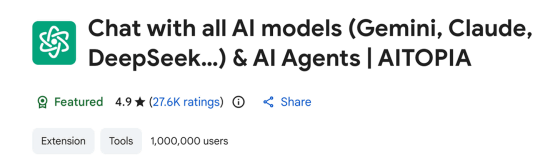
The Chrome extension in question was disguised as an existing extension released by a legitimate AI software company called
The official Chrome extension released by AITOPIA looks like this:
The Chrome extension in question only asked users to consent to the collection of 'anonymous, non-personally identifiable analytics data,' but instead stole various data without disclosing it to the user and sent it to the attacker's servers every 30 minutes. The data collected by the Chrome extension in question includes:
・Conversation data with AI
This includes 'proprietary source code and development queries shared with ChatGPT or DeepSeek,' 'discussions of confidential business strategies or company information,' and 'personal information, such as IP addresses, disclosed during conversations.'
- Browser history
This includes 'full URLs and browsing profiles collected from all Chrome tabs,' 'search queries containing sensitive keywords or research topics,' 'URL parameters that may contain session tokens, user IDs, and authentication information,' and 'internal URLs that reveal organizational structure and tools used.'
OX Security warned that 'this data could be used for corporate espionage, identity theft, targeted phishing attacks, or sold on underground forums. Organizations whose employees install these extensions could be unknowingly exposing intellectual property, customer data, and sensitive business information.'
At the time of writing, all of the Chrome extensions in question have been removed from the Chrome Web Store.
Related Posts:
in AI, Web Service, Security, Posted by log1h_ik