A survey by a former Google engineer reveals that ``Facebook and Instagram apps track users who tapped links in detail''

Meta, the owner of Facebook and Instagram, is using proprietary code to track users even after they click on links within their apps, according to the latest research by a former Google engineer. that's right.
iOS Privacy: Instagram and Facebook can track anything you do on any website in their in-app browser Felix Krause
https://krausefx.com/blog/ios-privacy-instagram-and-facebook-can-track-anything-you-do-on-any-website-in-their-in-app-browser
Meta injecting code into websites to track its users, research says | Meta |
https://www.theguardian.com/technology/2022/aug/11/meta-injecting-code-into-websites-visited-by-its-users-to-track-them-research-says
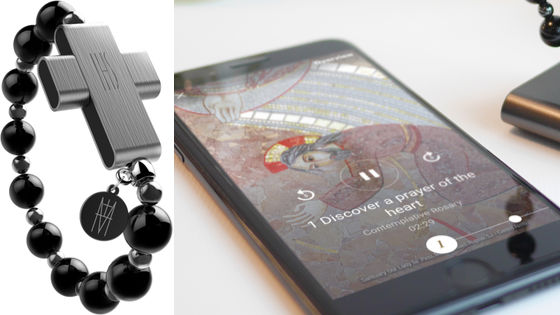
Meta's Facebook and Instagram apps open links in an in-app browser when users tap external links included in posts. Regarding this ``behavior when tapping an external link,'' Felix Krauss, a former Google privacy researcher, said, ``Instagram is showing up on all websites displayed in the in-app browser, including when you click on an ad. By inserting a tracking code, we are able to monitor all user actions, such as which buttons and links the user taps, selects text, takes screenshots, and fills out forms such as passwords. The traceable information also includes the user's address and credit card number.'
Klaus detects Meta's tracking code insertion by building a tool that can list all the extra code that browsers add to websites. In normal browsers and apps, Mr. Claus' tracking app will not detect the code. However, in apps such as Facebook and Instagram, up to 18 lines of code were detected. Regarding the detected code, Klaus says, 'It looks like a specific cross-platform tracking kit.' If you don't have apps like Facebook or Instagram installed, Meta will instead call a tracking code pixel to track what users are doing on the website. This will allow Meta to accurately profile every user's 'what they are interested in'.
Meta has never disclosed to users that it inserts tracking codes into two apps, Facebook and Instagram, and Klaus' research shows that WhatsApp, one of Meta's apps, has a similar feature. No tracking code was inserted. The act of ``adding extra code before the web page is displayed on the user terminal'', as Meta is doing, is called ``Javascript injection'' and is considered a type of malicious attack. I have a case. For example, cybersecurity firm Feroot describes Javascript injection as ``allowing an attacker to manipulate a website or web application to collect sensitive data, such as personally identifiable information or payment information.'' .
It is unknown when Meta started inserting tracking codes into its apps, but in 2021 Apple will allow users to choose whether to allow user tracking for advertising purposes `` App Tracking Transparency (ATT) '' By enabling , Facebook advertisers can no longer target ads as they used to . This ultimately caused Facebook's stock price to plummet by more than 20%. To combat this, Meta may have inserted tracking codes into two of its flagship apps.
Finally, the number of Facebook users decreased for the first time, the stock price crashed by 20% - GIGAZINE
In response, a Meta spokesperson said, ``This code was intentionally developed to work when the user selects ``Allow tracking'' on our platform.'' ``This code allows targeted advertising This code is designed to aggregate conversion events without adding pixels.' 'In-app browser For purchases made through Amazon, we ask for your consent so that we can save your payment information for autofill purposes.'
Related Posts: