Theft of virtual currency by North Korean hacker groups is increasing year by year & the method is getting worse

Cyber attacks from North Korea are steadily increasing, and in 2021, at least seven attacks on cryptocurrency exchanges and investment companies with a scale of 400 million dollars (about 46 billion yen) will be carried out from North Korea. It was said that. The amount of damage caused by hacking by North Korea has also increased by 40%.
North Korean Hackers Have Prolific Year as Their Unlaundered Cryptocurrency Holdings Reach All-time High --Chainalysis
https://blog.chainalysis.com/reports/north-korean-hackers-have-prolific-year-as-their-total-unlaundered-cryptocurrency-holdings-reach-all-time-high/
The graph below shows the breakdown of cryptocurrencies stolen by North Korea. Bitcoin (red) is less than a quarter of the total, and the proportion of Bitcoin is decreasing year by year. In contrast, Ethereum (yellow) is increasing year by year, with 58% of the cryptocurrencies stolen in 2021 being Ethereum. In addition, there are increasing cases where virtual currencies (blue) other than Ethereum's token standard ERC-20 (green) and Bitcoin Ethereum are stolen.
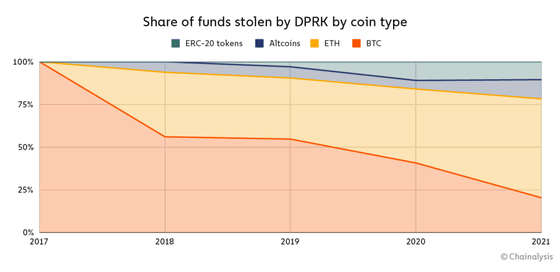
Stealing this ERC-20 and other cryptocurrencies also shows the deterioration of the tactics by North Korean hacker groups. ERC-20 and other cryptocurrencies are exchanged for Ethereum via Decentralized Transactions (DEX). This Ethereum is 'mixed' to increase anonymity by mixing multiple transaction data so that the flow of funds is not tracked. The mixed Ethereum will be exchanged for Bitcoin, which will be further mixed before being transferred to the new wallet.
In other words, by stealing various cryptocurrencies and tokens and putting them together, the North Korean hacking group is carefully laundering cryptocurrencies.
On August 19, 2021, the cryptocurrency exchange Liquid.com was accessed by unauthorized users on some of the cryptocurrency wallets under Liquid.com's control, and the ERC-20 was flooded with Ethereum.
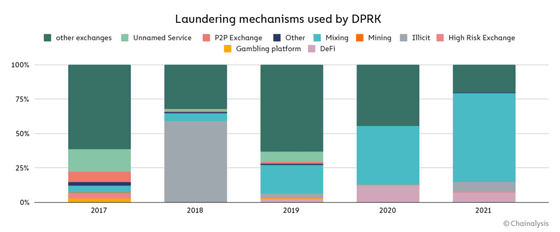
Since the purpose of laundering virtual currency is to prevent the identification of attackers, it is said that the frequency of attackers related to North Korea performing virtual currency mixing is increasing year by year. The bar graph below shows the percentage of work done in laundering, blue-green indicates mixing, and after 2019 you can see that mixing is rapidly increasing. This suggests that the North Korean hacker group has become more cautious with each passing year, according to Chainalysis.
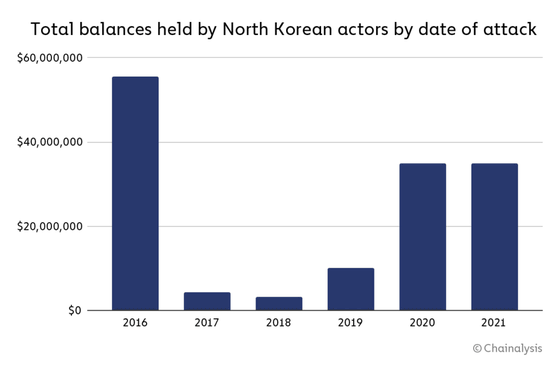
According to Chainalysis, the total amount of virtual currency stolen by North Korea is 170 million dollars (about 19 billion yen). There are multiple North Korean hacker groups, but it seems that only one group stole about $ 55 million (about 6.3 billion yen), which is about one-third of all the virtual currencies stolen by North Korean hackers. is.
However, this $ 55 million was due to an attack carried out in 2016, and it is said that it is still deposited in a specific wallet without being laundered. In other words, a cryptocurrency that has not been laundered for the next six years is sleeping in North Korea.
Chainalysis said, 'These data together reveal a nation that supports cryptocurrency crimes on a large scale. The organized and sophisticated North Korean government is through the Lazarus Group and other crime syndications. However, many cryptocurrencies are transparent, establishing themselves as an advanced and lasting threat to the crypto industry in 2021. By using blockchain analysis tools, compliance teams and criminal investigations Officials, hacking victims can track the movement of stolen money, keep up with the opportunity to freeze or seize assets, and hold malicious actors accountable for crimes. '
Related Posts:
in Security, Posted by log1i_yk







