The popular online FPS 'CS: GO' was found to be vulnerable to theft of account passwords via Steam's invitation system.

by
Counter-Strike: Global Offensive (CS: GO), an online competitive first-person shooter (FPS) produced and sold by Valve, which operates the game sales platform Steam, is an invitation system for online play on Steam. It was reported that a vulnerability was found in which the account password was stolen.
CSGO Exploit Allows Hackers to Steal Passwords | Game Rant
https://gamerant.com/csgo-stolen-password-exploit-hackers/
'Counter Strike' Bug Allows Hackers to Take Over a PC With a Steam Invite
https://www.vice.com/en/article/dyvgej/counter-strike-bug-allows-hackers-to-take-over-a-pc-with-a-steam-invite
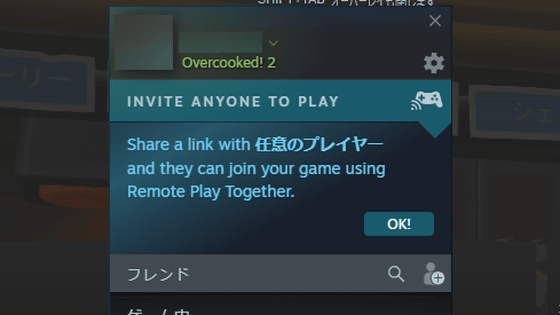
The vulnerability is reported by the white hacker group 'The Secret Club'. In 2019, Florian , a member of The Secret Club, discovered a remote code execution bug affecting Valve's game engine, Source Engine. A bug discovered by Florian can be used to attack users via Steam's invitation system.
The vulnerability in question is that 'accepting an invitation from an attacker steals the password of the user's Steam account', which can be executed not only in user chat but also in the community invitation system, and the attacker can There is a possibility of stealing passwords for a large number of accounts at once.
Years Ago Two, Secret Club Member Attofloesen_ Reported A Remote Code Execution Flaw Affecting All Source Engine Games. It Can Be Triggered Through A Steam Invite. This Has Yet To Be Patched, And Valve Is Preventing Us From Publicly Disclosing It. Pic.Twitter .com / 0FWRvEVuUX
— Secret club (@the_secret_club) April 10, 2021
At the time of writing the article, this vulnerability was discovered only in CS: GO, but according to Florian, this vulnerability may exist in all games that use Source Engine. Valve's popular multiplayer online battle arena game, Dota 2, also has a Source Engine game engine, which was upgraded to Source 2 Engine in 2015, so the bugs Florian discovered seems to have a huge impact. ..

by artubr
The Secret Club has reported this issue to Valve through its bug bounty platform, HackerOne , but has not received a reply from Valve and states that it has not been fixed at the time of writing.
'To be honest, I'm very disappointed because Valve almost ignores my report,' Florian said in an interview with the IT news site Motherboard. Motherboard also requested a comment from a Valve spokeswoman, but said he didn't respond.
In 2019, Valve pointed out that a zero-day vulnerability that could obtain administrator privileges on Steam's Windows version could affect more than 96 million people, but instead of ignoring the report, it found the discoverer It was reported that he was banished from the bug bounty program and later apologized.
Valve fully admits that it was 'wrong' to ignore Steam's zero-day vulnerability report-GIGAZINE

Related Posts: