What is 'Trillian' that can build a 'non-tamperable log system' developed by Google?

System logs are useful for auditing malicious third-party attacks and fraud, but there is no point in tampering with the logs themselves. ' Trillian ' developed by Google is an open source log platform that makes it difficult to tamper with such logs using a
An open-source append only ledger | Trillian
https://transparency.dev/
Trillian is one of the projects supported by Google-led ecosystem '

Logs, which play an important role in auditing third-party attacks and internal fraud, need to be highly tamper-resistant, not just stored. A tamper-resistant logging system has the advantages of 'preventing evidence destruction,' 'gaining the trust of auditors,' and 'allowing multiple parties to monitor each other's actions.' Specific examples of the need for a tamper-resistant logging system include package managers, servers, and financial institution transactions.
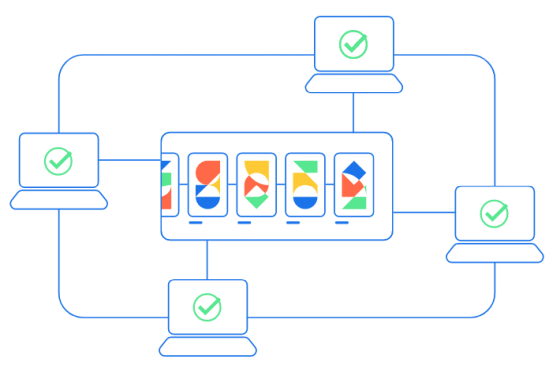
It is said that the most suitable for building a log system that is resistant to such tampering is the log platform 'Trillian' developed by Google that can only be added. Certificate Transparency lists the reasons for this, such as 'easy to install in existing systems', 'scaleable', and 'open source'.
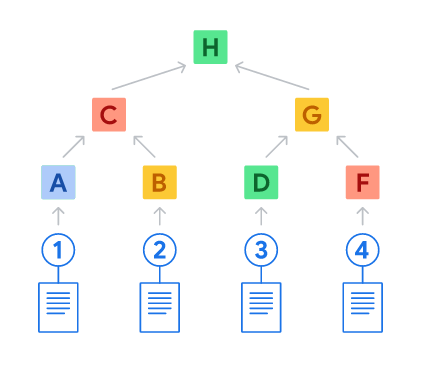
Supporting Trillian's tamper resistance is a data structure called a hash tree . The hash tree is characterized by achieving high tamper resistance by hashing the original data and connecting the hash values in a tree shape. Hash tree technology is also used in version control systems such as Git and Bitcoin.
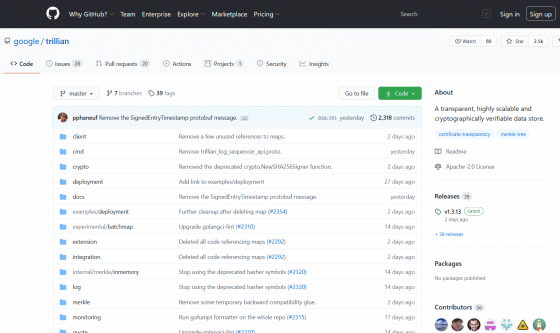
The source code for Trillian is published on GitHub and anyone can use it for free. In addition, Trillian build requires Go version 1.14 or higher, and you can use MySQL or MariaDB for data storage.
GitHub --google / trillian: A transparent, highly scalable and cryptographically verifiable data store.
https://github.com/google/trillian/
Related Posts: