The mysterious 'meow attack' where the contents of the database are almost deleted and only the cry of the cat is written is activated

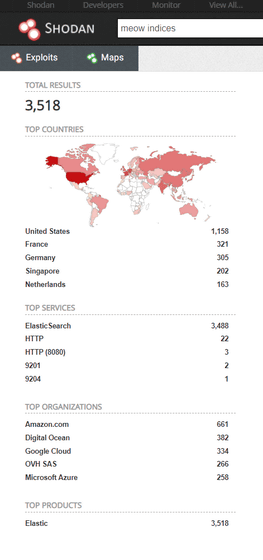
It has been reported that almost all unprotected databases on the Internet have been deleted, leaving only the meow call of a cat called ' Meow Attack .' At the time of writing the article, nearly 4000 databases had already been deleted by the meow attack.
New'Meow' attack has deleted almost 4,000 unsecured databases
Ongoing Meow attack has nuked >1,000 databases without telling anyone why | Ars Technica
https://arstechnica.com/information-technology/2020/07/more-than-1000-databases-have-been-nuked-by-mystery-meow-attack/
On July 1, 2020, security researcher Bob Diachenko discovered that the database of the Hong Kong-based VPN provider UFO VPN was exposed unprotected on the Internet. The database contained plaintext account passwords, VPN session tokens, VPN server IP addresses, connection timestamps, geotags, and more.
The database was protected by Mr. Diacenko's immediate warning to UFO VPN, but on July 20, 2020, the UFO VPN database was published again with another IP address. Moreover, the database that was republished with another IP address had the data difference as of July 19 added. Furthermore, on July 21, 2020, it was discovered that most of the contents of this database were deleted, leaving behind the string 'meow' at the end.
New Elasticsearch bot attack does not contain any ransom or threats, just'meow' with a random set of numbers.It is quite fast and search&destroy new clusters pretty effectively pic.twitter.com/F8Ke3CI64i
— Bob Diachenko (@MayhemDayOne) July 20, 2020
Also, the meow attack wasn't the only target of the UFO VPN database. At the time of article creation, there were more than 4000 databases that were meow attacked, including Elasticsearch , MongoDB , and Apache Cassandra . 'It seems that the meow attack is targeting all insecure databases published on the Internet,' Diachenko speculates and speculates that the meow attack may be scripted.
It's not uncommon for a malicious attacker to target a database that has been exposed publicly on the Internet, but in most cases, ransomware either charges a ransom or simply cleans the contents. Almost. The motive for the attacker to leave the word 'meow' like this time is completely unknown.
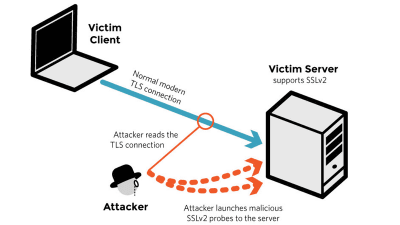
Security researcher Anthr@X reports on Twitter that the meow attack was through ProtonVPN . However, the information of other attackers is still unknown, and investigation is still ongoing at the time of writing the article.
The #meow attack is going thru @protonvpn ,not sure how many origin IPs there are.From the logs in MongoDB you can see it drops databases first then create new ones with $randomstring-meow @MayhemDayOne @BleepinComputer #infosec pic.twitter. com/49dnVOGyq7
— Anthr@X (@anthrax0) July 24, 2020
Diachenko said about this mystery of meow attack, because the 'defenseless as unsafe database on the Internet is easy to attack, would the malicious attackers are doing for fun. This meow attacks, cyber We are alerting industries and companies that ignore hygiene and lose customer data in an instant.'
Related Posts:
in Security, Posted by log1i_yk