It is pointed out that the 'new corona tracking function' of Apple and Google can 'collect data by a third party', and there is an opinion that there is a technically vulnerable side

Stop the Apple and Google contact tracing platform. (Or be ready to ditch your smartphone.) // Jaap-Henk Hoepman
https://blog.xot.nl/2020/04/11/stop-the-apple-and-google-contact-tracing-platform-or-be-ready-to-ditch-your-smartphone/
Apple and Google's 'New Coronavirus Tracking System' can track infected people with new coronavirus infection using Bluetooth Low Energy (BLE) and notify people suspected of heavy contact with the infected person Possible. In May 2020, APIs will be provided to health authorities to use the tracking system, and then the tracking system will be installed at the OS level in iOS and Android. The purpose and specifications of the new coronavirus tracking system can be understood by reading the following articles.
Answering questions about security and privacy that float with the ``new corona virus tracking system'' jointly announced by Apple and Google-GIGAZINE
User consent is required to operate the new coronavirus tracking system built into the OS. In addition, the tracking of infected persons is done using multiple keys so that Apple and Google cannot identify individuals, and the data stored in the central database is minimal. However, 'any decentralized structure can be a centralized structure,' Hoepman points out.
Even if the tracking system itself developed by Apple or Google has achieved decentralization of data, the API for tracking system released in May 2020 will be used by an application developed by a third party .. Therefore, it is possible for governments and companies that develop apps to collect data in one place, Hoepman said. Hoepman said, ``Apple pledged to treat our privacy politely, so we thought we could put our privacy and security under our control by purchasing an expensive iPhone, which is an illusion. It was.'

As an unintended use of the assumed tracking system, 'the police report the victim of the murder case as an infected person from the victim's smartphone and identify who was near the scene' 'Jealous partners and overprotection ``A guardian secretly installs an application on a tracked smartphone and tracks who they are meeting with,'' Hoepman said, ``If this system is a medicine for infection, the infection It's worse than the disease, and you should prepare to throw away your smartphone.'

Besides, cryptographer
If anyone can anonymously blast up keys, they can create a situation where there's GBs of data for all devices in the world to retrieve and compute.There would likely need to be some kind of rate limiting on a combination of stable IDs (phone number, (IP, etc) to prevent it.
— Moxie Marlinspike (@moxie) April 10, 2020
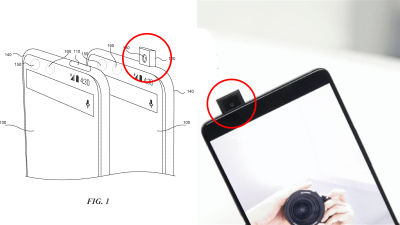
Also, in the comment section of Hacker News that introduces Mr. Hoepman's article, this tracking system was announced by Apple at `` WWDC 2019 '', a service that can be searched even on offline terminals by forming a network by Bluetooth `` Find Some say it's technically the same as ' My '.
What is the mechanism of 'Find My' function that Apple can announce the location even with offline terminals? -GIGAZINE

In the comments section, there are also comments such as 'Personal consent to use the system itself may be enforced by the government', 'Privacy is not so important now when facing the threat of the new coronavirus , Etc. are posted.
Related Posts: