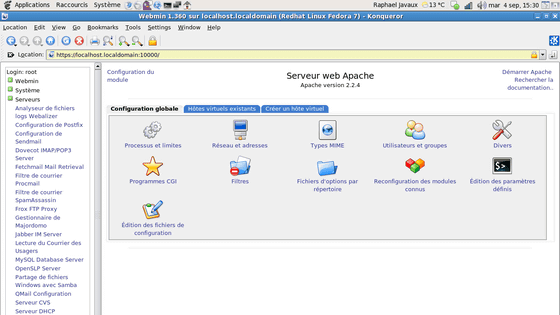
Server management tool 'Webmin' detects backdoor contamination
by Rapha222
As a UNIX OS server management tool, we found that the well-established ' Webmin ' was released with a backdoor included. Backdoors existed from version 1.890 to 1.920, and in 1.900 and later, the backdoor will not be abused unless the administrator changes the setting, but in version 1.890 the backdoor was usable by default That. Note that this was not a coincidence and we know that someone was deliberately adding a backdoor.
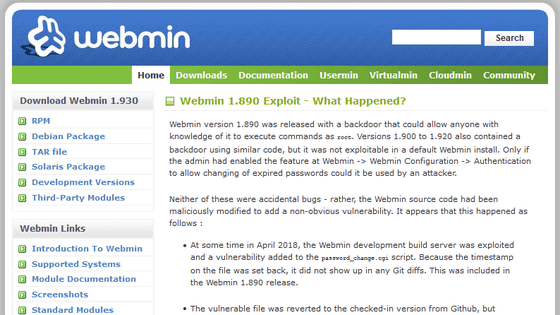
Webmin 1.890 Exploit-What Happened?
Backdoor Found in Webmin Utility | Decipher
https://duo.com/decipher/backdoor-found-in-webmin-utility
According to a survey by Webmin, in April 2018 there was an attack on the Webmin development build server, and a vulnerability was added to 'password_change.cgi'. At this time, it seems that the time stamp of the file was changed, so it was not recognized as a difference between Git commits. This is what happened with 'Webmin version 1.890'.
This vulnerability will be removed once, but in July 2018, 'Webmin version 1.900' will be re-malicious. At this time, a vulnerability was added to the code that was executed only when the administrator changed the 'Change Expired Password' feature.
The build server that was vulnerable to the attack was abandoned on September 10, 2018 and replaced with a new server, but the vulnerability was taken over because the file was copied from the original server, on August 17, 2019 “Webmin version 1.930” has been released, which fixes the vulnerability in response to the notification of the zero-day attack.
It is not the developer Jamie Cameron et al. Who added the vulnerability, but who did it is unknown.
Related Posts: