Valve fully acknowledges that it was `` wrong '' that it ignored Steam's zero-day vulnerability report

Despite the zero-day vulnerability reported on the Windows version of the game sales platform `` Steam '', the operating company Valve ignored this report, and the white hacker who found the vulnerability was replaced by Steam's bug bounty program Valve admitted that it was a mistake and announced a bug bounty program policy change.
Valve says turning away researcher reporting Steam vulnerability was a mistake | Ars Technica
Steam Patches LPE Vulnerabilities in Beta Version Update
https://www.bleepingcomputer.com/news/security/steam-patches-lpe-vulnerabilities-in-beta-version-update/
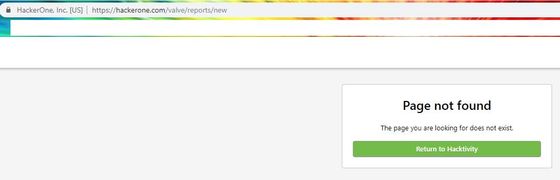
White Hacker Vasily Kravets operates HackerOne, a “bug bounty” service in which companies pay a bounty for zero-day vulnerabilities of Windows version Steam that `` can obtain administrator privileges without permission '' according to discovered vulnerabilities Reported to. However, Valve ignores Kravets' report. In addition, Mr. Kravets was banned from Valve's bug bounty program and banned, leaving no comments on all issues.
The series of issues is explained in detail in the following articles:
Why did White Hackers make public the zero-day vulnerability in Steam for Windows that could affect more than 96 million people? -GIGAZINE

However, Valve, on August 22, 2019, acknowledged the vulnerabilities related to the acquisition of administrator rights reported by Kravets. Valve also changed the bug bounty program policy that did not cover this vulnerability. At the same time, we announced that we will update the Windows version of Steam. Valve Marketing Director Doug Lombardi says 'This was a mistake' in relation to the removal of Kravets from Valve's bug bounty program.
by
The revised Valve HackerOne bounty program rule states that `` Running malware via Steam or running software with administrator privileges without notifying the User Account Control (UAC) dialog to obtain administrator privileges without permission '' “Bug to be activated” is considered to be within the policy.
Also, regarding Valve's bounty program rules, HackerOne was trying to bury the vulnerability itself in the dark by closing the thread so that Kravets could not report the vulnerability on their services. As for this matter, `` Prohibiting even the reporting of problems is a complete violation of the problem reporting policy adopted by Microsoft's International Standards Organization (ISO), is irresponsible to affected users, and discloses vulnerability Is being distorted by a commercial platform, ”Ars Technica severely denounces.
Kravets is still banned in the bug bounty program for Valve at HackerOne. Matt Nelson, who contributed to this vulnerability report, commented, “Money is not the purpose, but the purpose is to make the vulnerability known.”
Related Posts:
in Web Service, Security, Posted by darkhorse_log