The fingerprint verification system proved to be able to break through even 'master fingerprint' generated by machine learning

The pattern of fingerprints engraved on the belly of a human's finger differs according to the person, so it is often used for personal authentication systems that can be installed on PCs and smart phones. However, researchers at New York University and the University of Michigan report the surprising experimental results that it is relatively easy to break through by the master fingerprint " DeepMasterPrints " generated by machine learning.
[1705.07386] DeepMasterPrints: Generating MasterPrints for Dictionary Attacks via Latent Variable Evolution
https://arxiv.org/abs/1705.07386
Fake fingerprints can imitate real ones in biometric systems - research | Technology | The Guardian
https://www.theguardian.com/technology/2018/nov/15/fake-fingerprints-can-imitate-real-fingerprints-in-biometric-systems-research
Normally, the fingerprint authentication system does not read all the fingerprints, but only the fingerprints on the part placed on the sensor, as the user does not always put the finger on the sensor exactly the same way each time. Partial fingerprint scan has convenience while sacrificing some security partly.
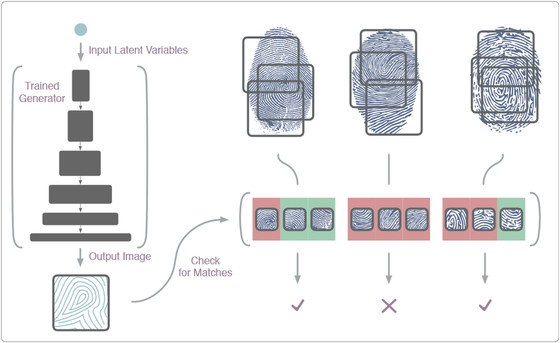
The research team thought that if you make a fingerprint that contains many features like fingerprints, the possibility of matching with different fingers will increase. Therefore, using a real fingerprint image as a data set to train a generative adversarial network (GAN), if it is a master key called "DeepMasterPrints" targeting a type of fingerprint sensor used in the latest smartphone I generated a "master fingerprint" at the image level.
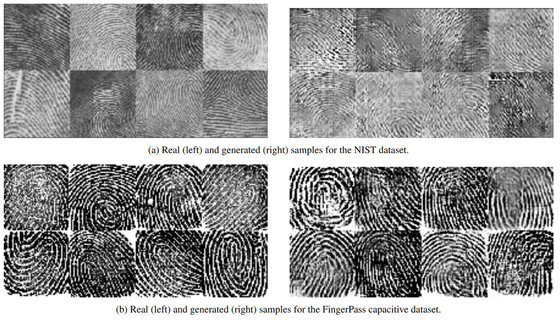
The research team prepared two kinds of fingerprint datasets to train the neural network. In the image below, the fingerprints on the top are "fingerprints read from the fingerprint image printed on the paper loaded into the fingerprint sensor", the underlying fingerprint is "Capacitive fingerprint sensor directly fingerprint Digital capture "is.
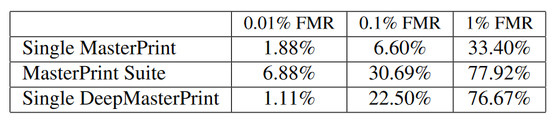
The security level of fingerprint authentication is defined by FMR (false match rate). FMR is the probability that it is erroneously judged as "the same finger" as a result of matching with a finger different from pre-registered fingerprints. The research team prepared fingerprint sensors with three levels of security level of FMR 0.01%, FMR 0.1%, FMR 1% and checked whether DeepMasterPrints can be used to clear fingerprint authentication.
As a result, it seems that the fingerprint sensor with 1% FMR with the lowest security level was able to deceive the sensor at a rate of 76%. The fingerprint sensor with FMR 0.1% stated by researchers, "the most realistic security level", said that 22% of the fingerprint sensor was able to pass through the authentication system. And with FMR 0.01% with the highest security level, it turned out that a mismatch occurred at a rate of 1.11%.
A researcher said, "From the results of this experiment, far more FMR has been calculated than what was expected from the original security level, and the idea of creating a fingerprint that becomes a master key like this time is surprisingly underestimated However, as with other security domains, it may be useful for creativity research on computers. "
Related Posts:







