When IoT products spread to homes, a terrible future of unlikely information leaks may come
"Mono's Internet (IoT)" terminals that create various services by connecting everything to the Internet are becoming popular. However, it has been pointed out that the spread of IoT terminals is inevitable to increase the risk of information leakage, and it can be realized by just looking at cyber attack examples in recent years.
Hackers Broke Into a Casino's High-Roller Database Through a Fish Tank | Digital Trends
https://www.digitaltrends.com/home/casino-iot-hackers-fish-tank/
Nicole Eagan CEO of Darktrace of security countermeasure company held in London, on the topic of security risk of IoT terminalExamples of casino high-rollers (customers) customer list leakedI mentioned. In this case, it is said that the customer list was leaked via the cloud using the security hole of IoT thermostat which controls the temperature of aquarium for ornamental fish installed in the casino and it got into the casino system. The casino never thought that the award-winning fish supplies would be a security hole, but Eagan said the IoT terminals that are not being handled by security holes are full of markets.
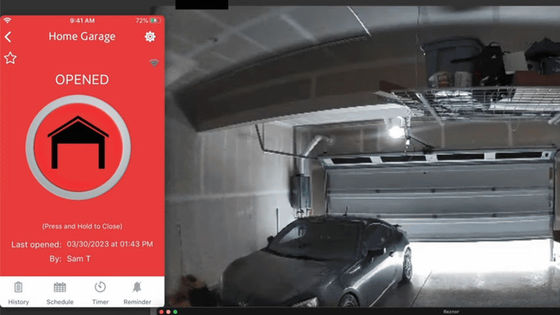
Even though it is unexpected that it is unexpected to be pierced by ornamental fish supplies completely unrelated, there are cases where a sufficiently foreseeable risk is realized. Advancing the IoT of household electrical appliances LG sells a robot vacuum cleaner with a camera "LG Hom - Bot", but the dangers of becoming an indoor surveillance device by being hijacked by this robotic vacuum cleaner are pointed out.

You can check the appearance of taking over the hit product "LG Hom - Bot" sold by over 1 million units and turning it into an indoor surveillance camera with the following movie.
LG HomeHack - Secure Your IoT - YouTube
The security hole of this LG Hom - Bot is reported to LG by the security company 's Check Point, and it is possible to take measures by updating the exclusive application SmartThinQ to version 1.9.2.3 or higher. According to Check Point, hackers seem to be targeting cybercriminals as IoT terminals that have the camera function of domestic IoT products as a big favorite, and have the function to shoot the indoor situation with a camera.

In addition, researchers at Ben Gurion University in Israel investigated whether passwords can be analyzed for 16 types of off-the-shelf IoT terminals.I could decipher the password of 14 terminalsAnd that. I reveal that most of this was connected to the botnet within 30 minutes. According to researchers, from the fact that most users do not change their default passwords, it is not necessary to perform advanced hacking such as disassembling and reverse-engineering the terminal, and according to researchers, It can be attacked just by checking the password.
Although it is a home IoT terminal that brings about the convenience enough to change life, there are vulnerabilities included in the terminal itself and the risk of information leakage can not be avoided by spreading users thanks to users who neglect security measures I have it.
Related Posts: